The Basics: Downlink vs. Uplink
Before understanding the maps, we must understand the direction of travel. In LTE, the “Road” is two-way, but the rules for each direction are different.
-
Downlink (DL): This is the path from the Network (Tower) to the Phone (UE).
- Analogy: This is like a TV station broadcasting or a server sending a file to you. The Tower is powerful and can shout loudly to everyone at once.
- Key Goal: To distribute information efficiently to either everyone (Broadcast) or one specific person (Unicast).
-
Uplink (UL): This is the path from the Phone (UE) to the Network (Tower).
- Analogy: This is you speaking back. Your phone has a small battery and weak power, so it must be very careful and organized when it transmits.
- Key Goal: To ask for permission to speak, and then send data without talking over other phones.
1. The Big Picture: The Three Layers of Channels
Think of the LTE protocol stack as a logistics company.
- Logical Channels (The “What”): This describes what is being shipped. Is it a control command? Is it a user’s web browsing data? Is it a system broadcast?
- Transport Channels (The “How”): This describes how the package is prepared for shipment. It deals with error correction, modulation, and packaging data into blocks.
- Physical Channels (The “Where”): This is the actual truck or plane. It describes the specific radio frequencies and time slots used to carry the data over the air.
2. Downlink Channel Mapping (Network to Phone)
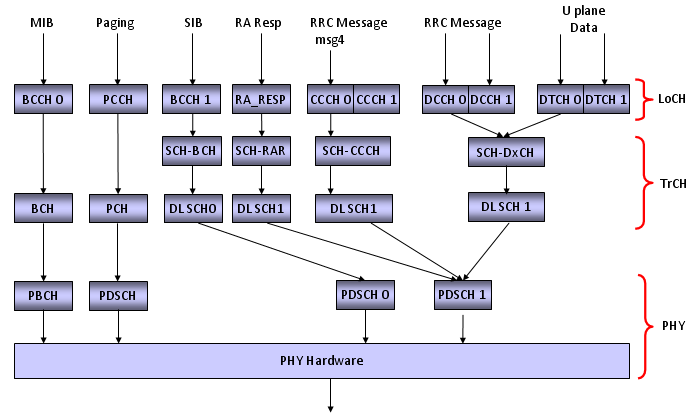 A. Broadcasting System Info (The “Announcement Speaker”)
When you turn on your phone, it knows nothing. The tower must announce “I am Verizon, I am Cell ID 5.”
A. Broadcasting System Info (The “Announcement Speaker”)
When you turn on your phone, it knows nothing. The tower must announce “I am Verizon, I am Cell ID 5.”
Logical Channel: BCCH (Broadcast Control Channel). This contains the MIB (Master Information Block) and SIBs (System Information Blocks).
- Path 1 (For MIB - The most critical info):
- BCCH BCH (Broadcast Channel) PBCH (Physical Broadcast Channel).
- Why? The BCH transport channel is designed to be super robust. Even if the signal is terrible, the phone must hear this.
- Path 2 (For SIBs - The detailed info):
- BCCH DL-SCH (Downlink Shared Channel) PDSCH (Physical Downlink Shared Channel).
- Why? SIBs are too large for the tiny PBCH lane. They are put on the “Shared” high-speed lane (DL-SCH) but marked as “Broadcast.”
B. Paging (The “Wake Up Call”) When someone calls you, the network must wake your phone up. Path: PCCH (Logical) PCH (Transport) PDSCH (Physical). The PCH transport channel is special—it supports “DRX” (Discontinuous Reception), allowing your phone to sleep and only wake up briefly to check for this specific message.
C. User Data & Signaling (The Actual Conversation) Once you are in a call or browsing the web, you use the “Shared” pipe.
- Logical Channels:
- CCCH (Common Control Channel): Used before you have a unique ID (during setup).
- DCCH (Dedicated Control Channel): Used for your specific signaling (e.g., “Handover to next cell”).
- DTCH (Dedicated Traffic Channel): Used for your actual data (IP Packets).
- Mapping: All three of these map to DL-SCH (Downlink Shared Channel) PDSCH.
- Detail: The DL-SCH is the workhorse. It supports HARQ (Hybrid ARQ), which means if a packet has an error, the transport layer instantly asks for a re-transmission.
3. Uplink Channel Mapping (Phone to Network)
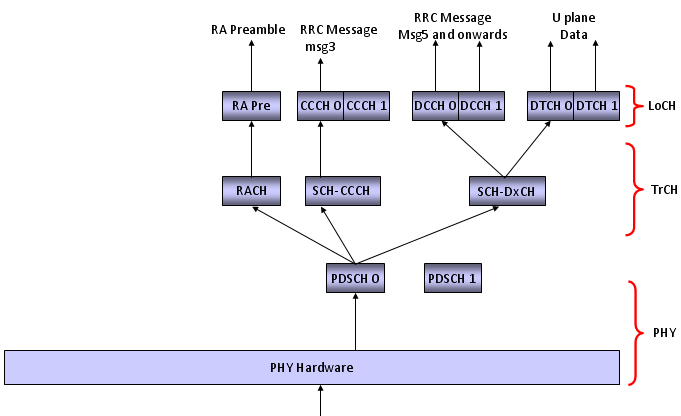 The uplink is simpler but has a unique channel for starting connections.
The uplink is simpler but has a unique channel for starting connections.
A. Random Access (The “Hand Raise”) When you first try to connect, you don’t have a digital connection yet. You only have a radio pulse.
- Process: You send a “Preamble” (a radio signature).
- Mapping: This skips the Logical and Transport layers. It goes directly to the PRACH (Physical Random Access Channel).
- Note: The document lists “RA Pre” mapping to “RACH” TrCH, but physically this is the PRACH.
B. The Standard Uplink (UL-SCH) Once the “handshake” is done, the phone behaves just like the downlink, but in reverse.
- Logical Channels:
- CCCH (Common Control): Used for the “RRC Connection Request” message.
- DCCH (Dedicated Control): Used for security and mobility messages.
- DTCH (Dedicated Traffic): Used for your Upload data.
- Mapping: All of these map to UL-SCH (Uplink Shared Channel) PUSCH (Physical Uplink Shared Channel).
5. Call Processing: The Timeline of Mapping
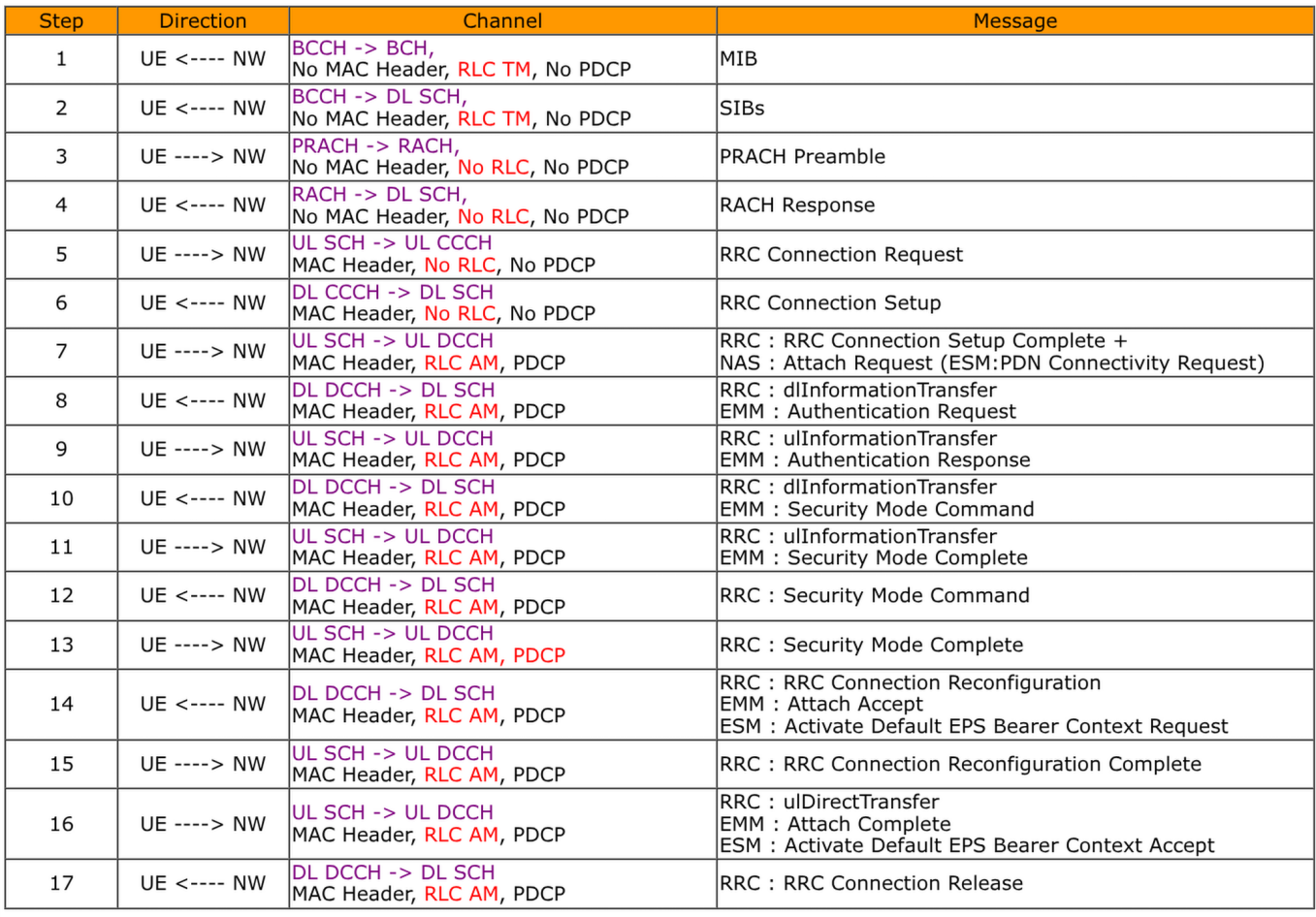
Phase 1: Idle (Listening)
- What happens: The phone is just listening.
- Active Channels:
- Config 1 & 2: You are reading MIB and SIB via the BCCH mapping.
- Config 8: You are listening for Paging via the PCCH mapping.
Phase 2: Access (Getting Attention)
- Step 1: You send a Preamble (PRACH).
- Step 2 (Config 3): The Network sends a “RACH Response.” Detail: This is a special message on the Downlink (DL-SCH) addressed to your random signature.
Phase 3: Setup (Establishing Identity)
- Step 3: You send “RRC Connection Request”.
- Channel: CCCH (Common Control).
- Why? The network doesn’t know who you are yet, so you use the “Common” channel.
- Step 4 (Config 4): The Network sends “RRC Connection Setup”.
- Action: The network assigns you a specific SRB1 (Signaling Radio Bearer 1).
- Change: You now switch from CCCH to DCCH (Dedicated Control Channel).
Phase 4: Security & Data (The Call)
- Step 5 (Config 5): Security Mode Command. Action: All data on the DCCH is now encrypted.
- Step 6 (Config 6): RRC Connection Reconfiguration.
- Action: The network opens the data pipes (DRBs - Data Radio Bearers).
- Change: You now have DTCH (Traffic) active alongside your DCCH.
- Result: You can now browse the internet while the network manages your connection.
Phase 5: Release (Ending)
- Step 7 (Config 7): RRC Connection Release. Action: The DCCH and DTCH are deactivated. [cite_start]The phone returns to Idle mode (Config 8), listening to BCCH and PCCH again.